Another great day of talks (Mixed in with some haphazard organisation and time keeping by EC-Council). I’m genuinely impressed with the level of professionalism and effort all the speakers have put into their presentations.
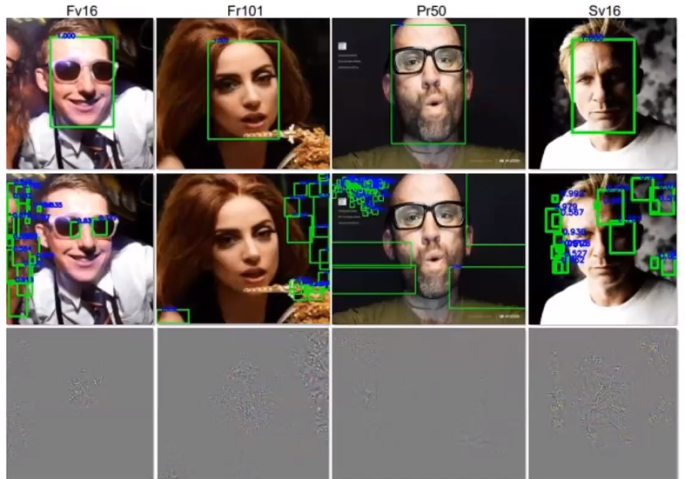
Starting off today was Alyssa Miller with a look at the current deep fake possibilities and a prediction that very soon it will be an issue handed over to cyber security professionals to protect organisations from being tricked by a deep fake of their company CEO. The brilliantly put together talk gives an overview of how generative adversarial networks create the deep fake to the current ways of spotting them, showing that researchers are in a very tricky situation whereby whenever they discover and publish a method for spotting deep fakes the creators instantly know which parts to improve.
Joe Gray gave us an overview of which metrics he thinks are important to focus on when running phishing simulations at an organisation and how to read the data in a way which allows you to create training plans for your users. Highlighting the need to make sure users feel comfortable telling you if they have messed up and how by using punishments for clicking on phishing e-mails you are hindering your own efforts at protecting the company.
Bryson Payne gave us a demonstration of how to reverse engineer software, starting from a beginners introduction to changing individual values in a game (Solitaire) through to a more technical example of how it’s possible to reverse engineer ransomware to extract the decryption keys. If you are new to software analysis or reverse engineering and not sure where to start this presentation will give you lots of resources including freeware tools to help you get started.
For beginners asking the first questions about how to get into pentesting the presentation by Phillip Wyle is for you. It starts off with some general descriptions and definitions of pen testing roles before getting into some very useful lists of resources such as books, websites, CTFS events and tools to help you start learning. Phillip’s career is focused on creating the next generation of pen testers so following his advice can’t be a bad idea.
As before, if you missed any of the event game codes they can be found on this page: https://urbansecurityresearch.com/2020/10/19/hacker-halted-2020-event-game-codes/